OTP authentication has become the default security layer for banks, delivery apps, fintech platforms, and almost every service that requires login or identity verification. But even though OTPs seem simple, they fail more often than teams expect late delivery, missing messages, customer lockouts, and even fraud risks.
Most OTP breakdowns come from a handful of mistakes that keep repeating across industries. The good news? Fixing these issues is straightforward once you understand where things typically go wrong.
This guide walks through the most common OTP mistakes, why they happen, and exactly how to fix them based on real-world patterns observed across global operators and high-volume platforms.
D7 Networks is mentioned where relevant, purely from a technical and operational standpoint.
Why OTP Failures Happen More Often Than You Think
A customer tries to sign in, waits for the code… and nothing arrives.
A bank issues OTPs that get filtered.
A mobility app sends codes, but users see “invalid OTP” even when typing correctly.
These problems frustrate customers, create support overhead, and damage trust.
Most failures stem from:
- Routing issues
- Sender ID restrictions
- Weak OTP formatting
- Regulatory blocks
- Misconfigured verification logic
- Missing fallback channels
Let’s break down the biggest mistakes so you can avoid them.
1. Using the Wrong Sender ID
One of the most common reasons for OTP failure is using a sender ID that local operators reject.
Why it happens
Every country has different rules:
- Some require numeric sender IDs
- Some require pre-registration
- Some rewrite alphanumeric senders to generic numbers
- Some block anything unregistered
When businesses send OTPs with the wrong type of sender, messages get filtered or rewritten causing late delivery or no delivery at all.
How to fix it
- Always check country-specific requirements
- Use numeric sender IDs in stricter markets
- Pre-register sender IDs where needed
- Use operator-approved templates
D7 Networks automatically selects the right sender format per country, reducing guesswork.
2. Overloading OTP Messages with Extra Text
A common mistake: trying to add branding, legal lines, URLs, or promotional wording inside an OTP message.
This leads to:
- Filtering
- Slower delivery
- Customers missing the actual code
Why operators filter long OTP messages
Telecom systems expect OTPs to be short, predictable, and purely transactional.
Fix it
Keep OTP messages minimal:
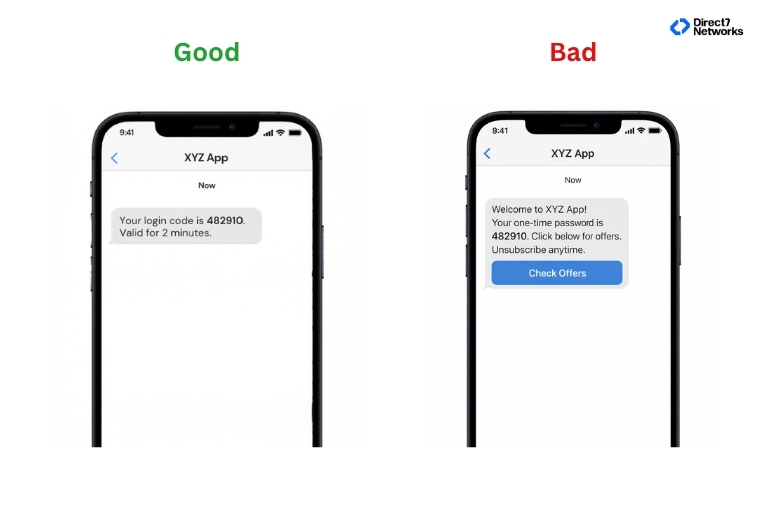
Simplify → Deliver faster.
3. No Retry Logic or Fallback Channel
Most OTP failures are temporary:
Network congestion, operator throttling, DND restrictions, or device issues.
Common mistake
Sending one OTP and assuming it will reach.
Fix it
A healthy OTP system includes:
- Retry with alternative routes
- Switch channel if SMS fails (WhatsApp or voice call)
- Allow the user to request a fresh code without penalty
Platforms using D7’s routing have automatic failover to multiple carriers, improving reliability.
4. Incorrect OTP Expiry & Validation Logic
You’d be surprised how many apps implement validation incorrectly.
Common mistakes
- OTP is valid for too long
- OTP expiring too quickly
- Accepting expired OTPs
- Server and client time mismatch
- Reusing old OTPs
Fix it
- Ideal expiry: 1–3 minutes
- Only last OTP should be valid
- Store OTP hashes, not raw codes
- Enforce time sync between client & server
Short expiry = fewer fraud risks + smoother UX.
5. Poor Phone Number Validation
Many OTP failures happen before the message is even sent.
Example mistakes
- Accepting invalid number formats
- Missing country code detection
- Not blocking VOIP or risky numbers where required
Fix it
Use number validation before sending OTP:
- Check country format
- Identify line type (mobile / landline)
- Correct missing +country codes
D7’s Number Lookup API is often used for this step to reduce wasted OTP traffic.
6. Mixing Promotional Text with OTP Traffic
Some businesses try to sneak marketing text into OTP messages, thinking “one message won’t hurt.”
Operators almost always filter this.
Fix it
OTP = purely transactional.
Promotional = separate template and sender.
This single change dramatically improves deliverability.
7. Using Weak OTP Formats
Mistakes include:
- Using predictable patterns (123456, 000000)
- Using long or complicated alphanumerics
- Generating OTPs without proper randomness
Fix it
Use:
- 4–6 digit numeric OTPs
- Cryptographically secure randomness
- Consistent format per region
Fast to read + easy to type = fewer support tickets.
8. Not Considering Local Regulations
Some countries require:
- Template registration
- Sender ID registration
- Pre-approval of content
- DND checks
If you skip this, OTPs get filtered.
Fix it
Before expanding to a new region:
- Check local SMS rules
- Use pre-approved templates
- Register sender IDs
- Follow character restrictions
This is especially important in markets like India, GCC, Africa, and parts of the Middle East.
Conclusion: OTP Success Comes from Fixing a Few Core Issues
OTP delivery isn’t magic it’s engineering, compliance, and smart message design.
Most problems come down to:
- Wrong sender IDs
- Weak templates
- Missing fallback channels
- Poor validation logic
- Ignoring country rules
Fix these, and your OTP success rate jumps dramatically.
Start by:
- Simplifying message content
- Choosing the right sender ID
- Adding retries and fallback
- Validating phone numbers
- Cleaning up verification logic
Small improvements → major reliability gains → happier users.