Fraud today moves fast. Customers expect everything to be instant, and attackers take advantage of that speed. They exploit weak onboarding flows, outdated authentication systems, and slow manual checks. That’s why more teams are rebuilding their security around something simple but very effective: real-time OTP verification.
A one-time password isn’t a new idea, but the way businesses use it has changed. Modern OTP flows are faster, smarter, and tightly connected to risk signals. When designed well, OTP becomes more than a password,it becomes a real-time gatekeeper that catches bad behavior before it turns into loss.
This article breaks down how today’s teams use OTP to prevent fraud, what works, what breaks, and the best practices that truly matter in 2026.
Why OTP Still Matters in a World Full of Fraud
Digital fraud spikes every time businesses make onboarding easier. Attackers create fake accounts, test stolen numbers, reuse leaked credentials, and exploit systems that don’t verify identity at the right moment. OTP solves this by adding a real-time check that asks: Is this person actually in control of this phone number right now?
Teams use OTP verification for three reasons:
- Stops account farming - Fraud farms often create hundreds of accounts in minutes. OTP forces them to use real devices, increasing their cost drastically.
- Verifies ownership instantly - A phone number is one of the strongest “possession factors” in authentication.
- Adds friction only for suspicious attempts - Good users move through quickly; suspicious ones get blocked or challenged.
When attackers rely on speed, even a three-second delay from OTP can break their workflow.
How Real-Time OTP Verification Works Behind the Scenes
A modern OTP flow is not just “send a code and check it.” It usually includes:
1. Number Formatting & Pre-Checks
The system first identifies whether the number is valid, reachable, or risky.
Many platforms also run number lookup to check if the number is:
- VoIP (high risk for fraudsters)
- Recently activated
- Swapped recently (SIM-swap risk)
- Invalid or inactive
This pre-check stops fake numbers before the OTP is even sent.
2. Intelligent Routing (SMS, WhatsApp, Voice)
To avoid delays, smart OTP platforms route based on:
- User location
- Channel performance
- Failover rules (e.g., SMS → WhatsApp → Voice)
D7 Networks, for example, offers multi-channel failover so the user is verified even if one network route stalls.
3. Delivery Status & Latency Monitoring
Fraud teams rely on real-time delivery receipts to detect patterns:
- If the same IP requests multiple OTPs
- If OTPs fail repeatedly
- If the number is already blacklisted
4. Code Verification + Risk Scoring
The moment the user enters the code, verification tools check:
- Time taken to enter OTP (bots are instant)
- IP/device fingerprints
- Geolocation mismatches
- OTP request frequency
The result is a simple approve/deny signal, but backed by multiple layers beneath.
Where OTP Stops Fraud Before It Happens
1. Fake Account Creation
Fraudsters often register hundreds of emails or phone numbers to redeem offers or run scams.A real-time OTP stops this by forcing unique device ownership.
Example:
A gaming app noticed large volumes of fake account signups using virtual numbers. Switching to OTP with number lookup reduced fraud attempts by 68% in the first week.
2. Payment & Checkout Fraud
Before confirming:
- High-value purchases
- Wallet withdrawals
- Saved card updates
OTP acts as a final user confirmation.
Attackers who hijack accounts with stolen credentials get blocked at this step.
3. SIM-Swap & Account Takeover Attempts
Modern fraud depends heavily on taking over a user’s SIM before draining wallets.
Teams now:
- Run SIM-swap checks
- Trigger OTP
- Compare device/IP against past logins
Any mismatch triggers a block or manual review.
4. Login Attacks and Credential Stuffing
When an attacker uses leaked usernames/passwords to break into accounts, OTP breaks the chain.
Even if they have the password, they won’t have the phone.
5. Suspicious Activity Verification
Businesses now trigger OTP dynamically when behavior looks “off.”
Examples:
- Login from an unusual region
- Device never seen before
- Sudden change in account details
- Repeated 2FA failures
OTP becomes a real-time checkpoint.
Best Practices Teams Use to Make OTP Fraud-Proof
1. Use Multi-Channel OTP (SMS + WhatsApp + Voice)
Relying on one channel is risky. Users may face:
- Network delays
- DND restrictions
- Carrier filtering
Smart teams create a fallback sequence.
Example fallback:
SMS → WhatsApp → Voice Call.
2. Keep OTP expiry short (30–60 seconds)
Long expiry windows give attackers more time to abuse codes.
Short expiry means:
- Faster verification
- Less exposure to interception
3. Block high-risk numbers upfront
Using number lookup, teams automatically reject:
- VoIP numbers
- Disposable numbers
- Recently swapped SIMs
This alone cuts a huge portion of fraud attempts.
4. Rate-limit OTP requests
Implement:
- Maximum of 3 attempts per hour
- Cooldown for repeated failures
- IP/device throttling
This stops bots and scripts from abusing OTP endpoints.
5. Use templated messaging for carrier compliance
Carriers filter suspicious messages.
Clean templates ensure OTPs always get delivered.
Direct7 Networks, for example, handles template compliance automatically across regions.
6. Log every event for forensics
Teams track:
- Device ID
- IP address
- Time to complete OTP
- Location mismatch
- Number validation logs
This data helps refine fraud models and block future attempts.
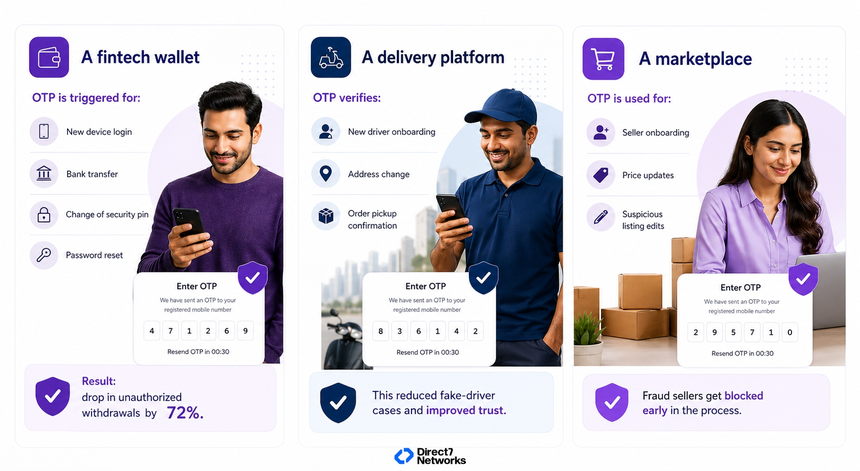
Real-World Examples of OTP Preventing Fraud
Where Teams Go Wrong (and How to Avoid It)
Some common mistakes:
Sending OTP only via SMS
→ If SMS fails, users get stuck.
Allowing unlimited OTP retries
→ Bad actors exploit this.
Ignoring number intelligence
→ VoIP and disposable numbers slip in.
Treating OTP as “one-time setup”
→ Fraud changes monthly; OTP rules must evolve.
The best teams treat OTP as a living system, refined regularly based on fraud patterns.
Conclusion: OTP Is Still One of the Most Effective Anti-Fraud Tools If Used Smartly
Fraud has become faster, smarter, and more automated, but so has OTP. Today’s verification flows combine real-time routing, number intelligence, device checks, and risk scoring to stop fraud before it costs money.
Whether you're protecting user onboarding, payments, or day-to-day account activity, a well-designed OTP flow is one of the simplest and most powerful defenses available.
Start small. Lock down high-risk moments first. Expand and adjust as patterns change.
When used thoughtfully, OTP becomes more than a code; it becomes your team’s real-time fraud shield.